AirSnitch: Lateral Movement from Guest Wi-Fi to Internal Network
- February 28, 2026
- 8 mins
- Research
TL’DR
AirSnitch does not rely on a single novel break. It chains older primitives across Wi-Fi encryption, switching, and routing assumptions to restore full MitM capability even when client isolation is enabled.
Why This Matters
For years, many teams treated client isolation as a reliable boundary: turn it on, stop lateral client abuse, reduce MitM risk.
AirSnitch shows that assumption is weak when controls are evaluated in isolation. The practical issue is chaining:
- Shared key abuse at the wireless layer
- Injection paths across Layer 2 and Layer 3
- Identity desynchronization across MAC, IP, AP, and SSID context
Individually, these are familiar. Combined, they restore attack paths many defenders considered “legacy.”
The Core Shift: From Single Exploit to Attack Composition
The NDSS 2026 research frames the problem as incomplete, non-standardized implementations of client isolation across vendors and deployments.
Key result: tested environments were vulnerable to at least one bypass path, and the bypasses were composable into end-to-end MitM.
This is why AirSnitch feels important: the novelty is not one bug, it is reliable composition across control boundaries.
How the Chain Works
At a high level, the attack family combines multiple primitives:
1) Shared Key Abuse (GTK/IGTK Context)
- Broadcast or management-plane protections rely on shared material in many deployments
- Insider access can be enough to inject or manipulate traffic paths in ways isolation was expected to block
2) Gateway Bouncing
- Packets are crafted with victim IP intent while using gateway-facing Layer 2 routing behavior
- If isolation logic is strict at one layer but weak at another, forwarding behavior can still deliver attacker-controlled traffic
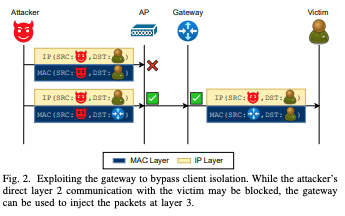
Gateway bouncing bypasses direct client-to-client blocking by forcing packet traversal through the gateway path.
3) Port Stealing / Identity Spoofing
- By abusing weak cross-layer identity binding, attackers can impersonate endpoints and influence uplink/downlink handling
- Combined with injection, this can yield practical bidirectional MitM positioning
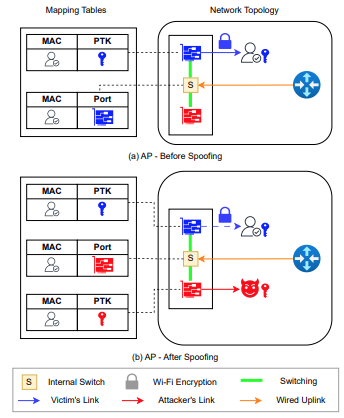
The spoofing stage poisons MAC to port association so victim traffic is redirected through attacker-controlled links.
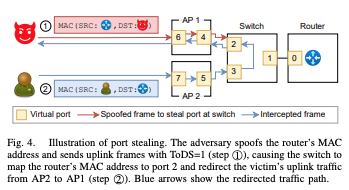
Port stealing then maintains interception by forcing the switch to relearn critical addresses on attacker-facing paths.
The broader point is that “client isolation enabled” is not equivalent to “client-to-client attack impossible.”
Old Attacks, New Reliability
What came back into fashion is not ARP spoofing by itself, nor simple rogue AP tradecraft by itself. It is operational chaining:
- Legacy traffic-manipulation ideas
- Modern Wi-Fi feature sets
- Real-world policy gaps between wireless, switching, and routing layers
This is exactly the type of recombination that tends to evade teams focused on single-control validation.
Defensive Takeaways
Cisco’s March 2026 guidance is consistent with the research outcome: treat client isolation as local hardening, not a complete trust boundary.
Practical defensive priorities:
- Prefer identity-based access over shared passphrase models for enterprise use cases
- Apply Layer 2 and Layer 3 anti-spoofing controls (for example DHCP snooping, DAI, source validation, anti-hairpin ACL logic)
- Instrument and forward wireless + switching telemetry into SIEM pipelines
- Alert on duplicate MAC/IP behavior, anomalous management traffic, and impossible client movement patterns
- Keep transport-layer encryption (TLS) enforced so interception does not automatically become data compromise
Mitigation is less about one patch and more about enforcing cross-layer consistency.
Closing Thoughts
AirSnitch is a reminder that attack evolution often looks like recombination, not reinvention. When older primitives are chained across weakly-coupled controls, “enabled security features” can still collapse under realistic adversary workflows.
The lesson for both red and blue teams is the same: test security assumptions as an end-to-end system, not as isolated toggles.