Coruna: Analysis of a Chained iOS/macOS Exploit Kit
- March 11, 2026
- 5 mins
- Exploit Reversing
TL’DR
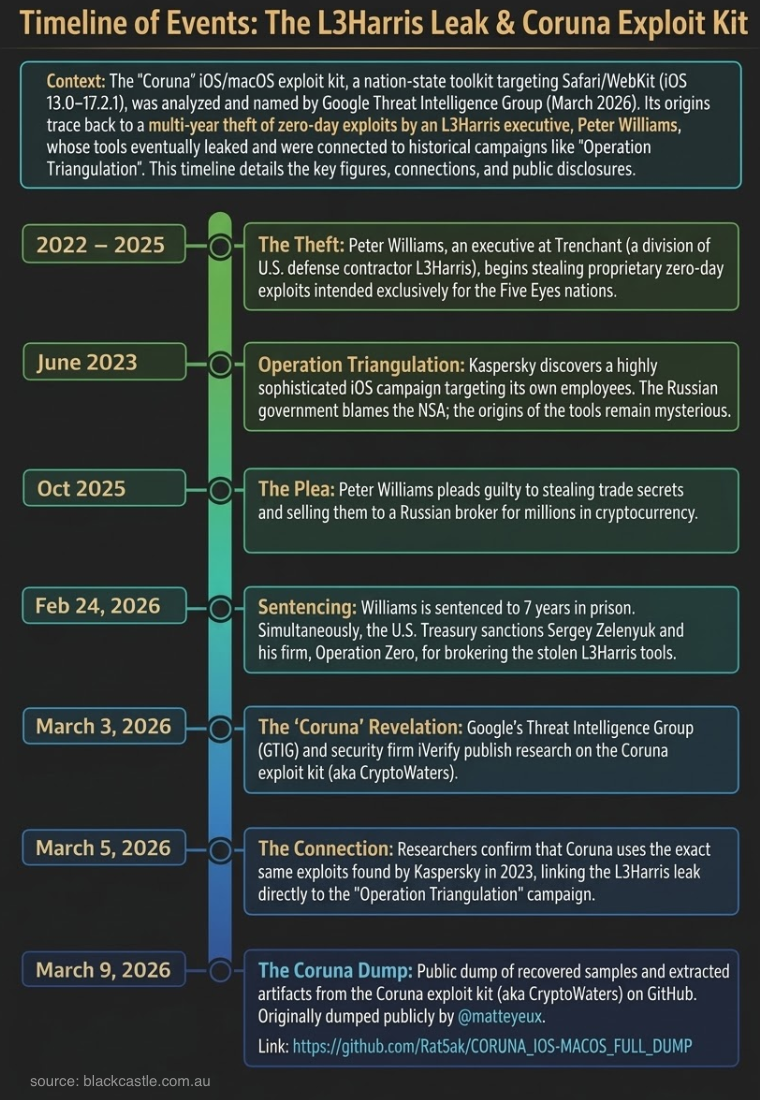
Coruna is a strong example of old attack ideas regaining impact through chaining: watering-hole delivery, heavily obfuscated browser-stage JavaScript, multi-path WebKit exploitation, and a follow-on kernel stage. The March 2026 artifact releases make this understanding concrete.
What the Recovered Artifacts Show
Using the released dump and technical analysis repos, the chain is no longer just IOC-level reporting. We can inspect structure and execution flow directly.
1) Browser Stage Is a Modular Exploit Framework
Recovered sets include 28 JavaScript modules, platform split paths (ios_*, macos_*), fallback loaders, and deobfuscated payload variants. The module system uses hash-based import/registration patterns and runtime decoding, which complicates simple static signatures.
2) Multiple Exploit Paths Feed a Shared Post-Exploitation Core
Public analysis describes separate paths converging into a shared memory primitive and common downstream logic:
- macOS-focused paths (including JIT-related routes)
- iOS-focused path (including OfflineAudioContext/SVG abuse patterns)
- fallback trigger logic when primary paths are unavailable
This is important operationally: defenders are not facing one brittle exploit, but a framework with path diversity.
3) Staging and Payload Engineering Are Built for Resilience
Recovered artifacts include extracted WebAssembly modules, Mach-O payload components, encoded blobs, and shellcode stages. GTIG reporting also notes delivery via hidden iframe chains and domain infrastructure built to rotate lures while preserving exploit delivery patterns.
Techniques and Tactics (Why Old Tradecraft Still Works)
Coruna does not win by one “new trick.” It wins by composing known ideas across layers:
- Initial access: watering-hole style web compromise and hidden iframe delivery
- Execution: browser-native JavaScript and WebAssembly staging
- Defense evasion: obfuscated module loaders, runtime string decode, multi-path fallback logic
- Privilege escalation: browser-to-kernel chaining with a kernel-stage follow-on exploit path
- Command and control: web-native staged retrieval over standard HTTPS patterns
The tactical lesson is straightforward: isolated controls can look healthy while cross-layer composition still succeeds.
Defender-Focused Takeaways
- Treat browser telemetry as an exploit surface, not just “web traffic”
- Hunt for staged loader behavior (many small modules, runtime decode, conditional pathing)
- Correlate web process anomalies with kernel/driver activity and post-exploitation process behavior
- Prioritize rapid patch validation for Safari/WebKit and kernel-exposed components
- Assume exploit kits will keep reusing proven primitives in new combinations
Closing Thoughts
The March 2026 Coruna disclosures are a useful reminder: major capability shifts often look like recombination, not reinvention. Once artifact-level data is public, defenders should pivot from campaign headlines to chain-level detection engineering.